Video content and carousels on Instagram are the most popular formats for brands to make edutainment , or educational entertainment. Especially videos, also thanks to the increase in popularity of Reels on Instagram, are perfect for engaging and educating users on multiple topics. Some statistics ha...
From 9 January 2022 , the owners of all websites will have to comply with the new Cookie Guidelines issued by the Privacy Guarantor on 10 June 2021. The provision indicates which rules to apply to reading and writing operations within a user's terminal, with reference to the use of cookies and other...
Instant messaging is, to date, the preferred means of communication for most people, both in personal and business spheres. Reports and statistics confirm this: the reasons are linked to the greater speed and ease of communication combined with free of charge, ease of use and immediate availability ...
What is meant by privacy policy, why every website should adopt a disclosure that clearly illustrates the ways in which user data is collected, used and managed and what the penalties are foreseen in case of failure to comply with the GDPR Those who manage blogs, e-commerce or Internet sites have a ...
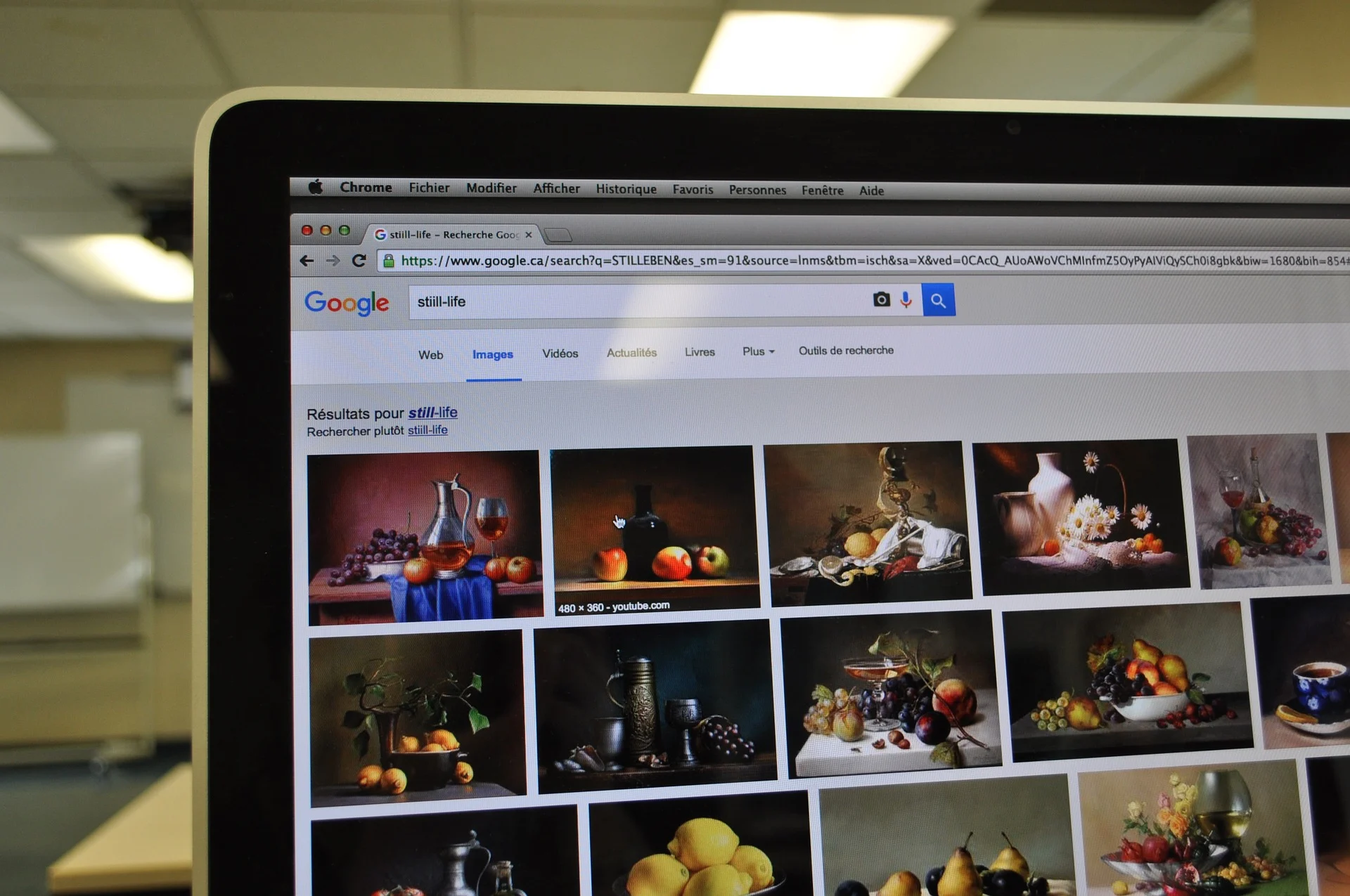
Did you know that Google Images also allows you to search for images by simply uploading a photo? Google is constantly optimizing its search engine to make it increasingly effective and close to user requests and with this interesting feature, it satisfies all those who wanted a solution to find sim...
How do you make a good podcast ? Everyone talks about podcasts and everyone, at least on paper, can become a podcaster in an instant. Today, the podcast is the shortest route to truly effective personal branding . You can use them for content marketing , to tell stories, inform, educate, engage . It...
If you want to know if hackers have stolen your passwords and email addresses that allow you to log into websites, Firefox Monitor makes it easy to find out, even automatically. First of all, a necessary premise, I used the word " hacker " only because in the common imagination it is hackers who do ...
Despite efforts to defend our data, there is still a lot of digital identity theft. In fact, if in real life it is infrequent but possible for this to happen, in the world of the web it is a much more widespread thing. Just stop and think about how many times you've simply heard of someone who had t...
Have you always wondered if you can customize recent Office files and recover unsaved Word, Excel and Powerpoint files? Of course yes. In the versions of Office, starting from 2010 up to the most recent ones, particularly interesting features have been added that allow users to recover even files th...
If you are a designer, you work with images to define and convey messages. Colors are a fundamental part of these images and color rendering (and therefore color management) is a crucial node in creating works that satisfy you first and that elicit an adequate response from the people to whom you co...
Rootkits are a serious threat, a particular form of malware that is often difficult to detect within a computer system and even more difficult to eliminate. Once inside the system, they provide a great deal of power to the hackers who run them, such as permission to access them at will, without the ...
Doing them is good and right. But what are the right questions? Who should we do it to? And above all, how should we position them? Three questions [and more] to answer the question mechanism. Knowledge - the deep one - feeds on doubt to find form . The question, more than Socratic, is logical: we c...
We have often talked about the importance of defining your Buyer Persona ( here , again here and here ), to define and choose the customers you want to relate to. A key element for increasing the business of your company or business and an indispensable figure for an effective Inbound Marketing stra...
Many of the requests often made to me by clients may seem strange, but they don't just concern advertising or marketing, but also information technology, the use of Office and the search for solutions to management problems. For this reason, with this post, I have decided to inaugurate a new series ...
Documenting home life and capturing family moments is what inspired many of us to pick up a camera. But when we picked up a camera, we discovered how challenging it is to capture those moments. Below you'll find some tips that, in the end, are what I've used over the years to capture my images, my m...
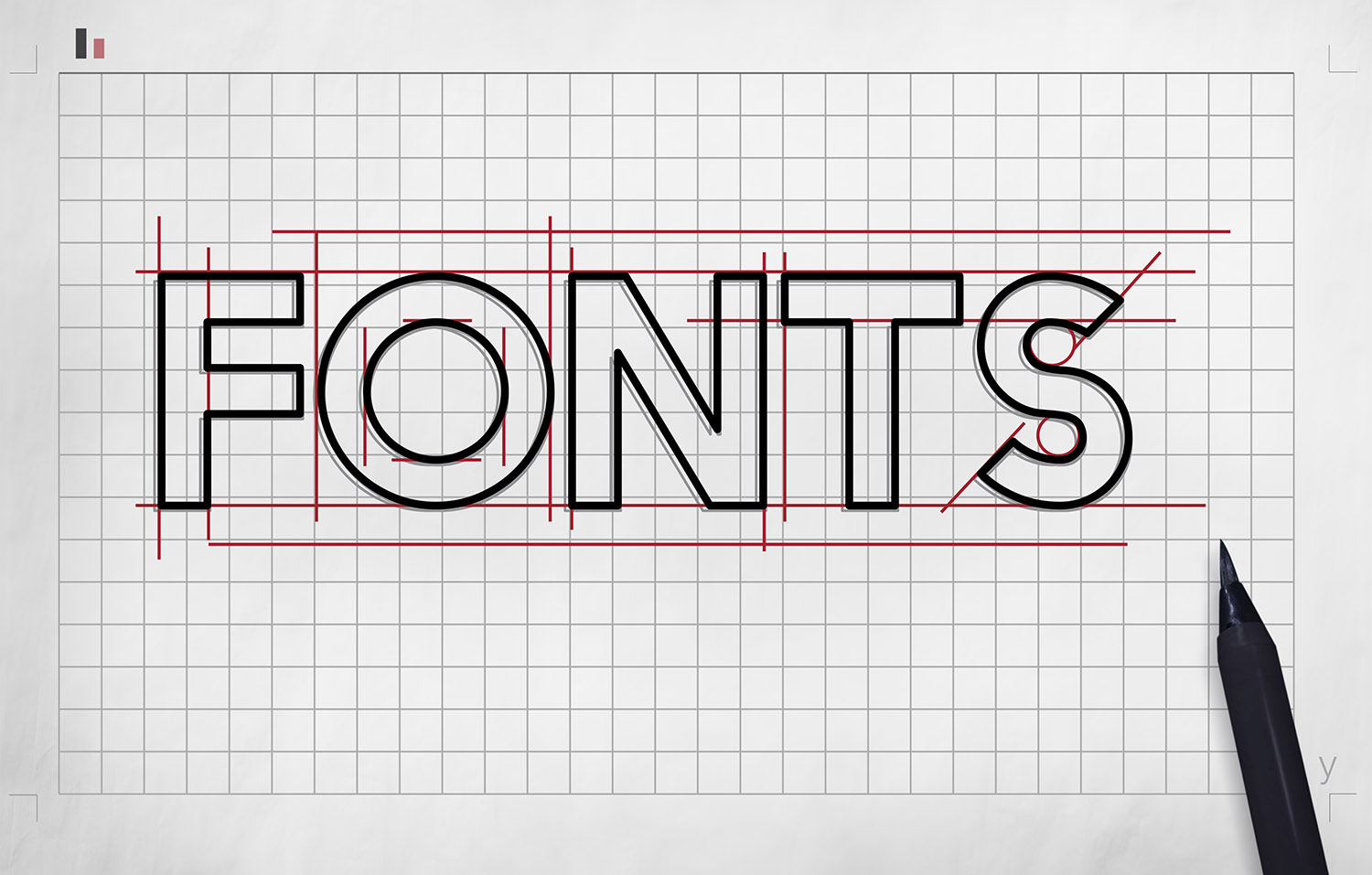
In this article I have introduced the subject of fonts and typography. I also told you about serif and sans serif and therefore about font families, how they are divided and how it is preferable to use them. As I anticipated in the previous article, there are a lot of other things to know about the ...
What is a font? And how do you use fonts? How can you create quality typographic projects, using fonts in the best way? This article aims to be the answer to this and many other questions that many young designers ask themselves every day. A first guide that seeks to create a complete introductory r...
When creating a Buyer Persona it is necessary to go beyond his profile, where by profile we mean the demographic, sociographic elements, related to education, company role, spending power, to instead go deeper, investigating new factors and unknown, to find out how, when and why the purchasing decis...
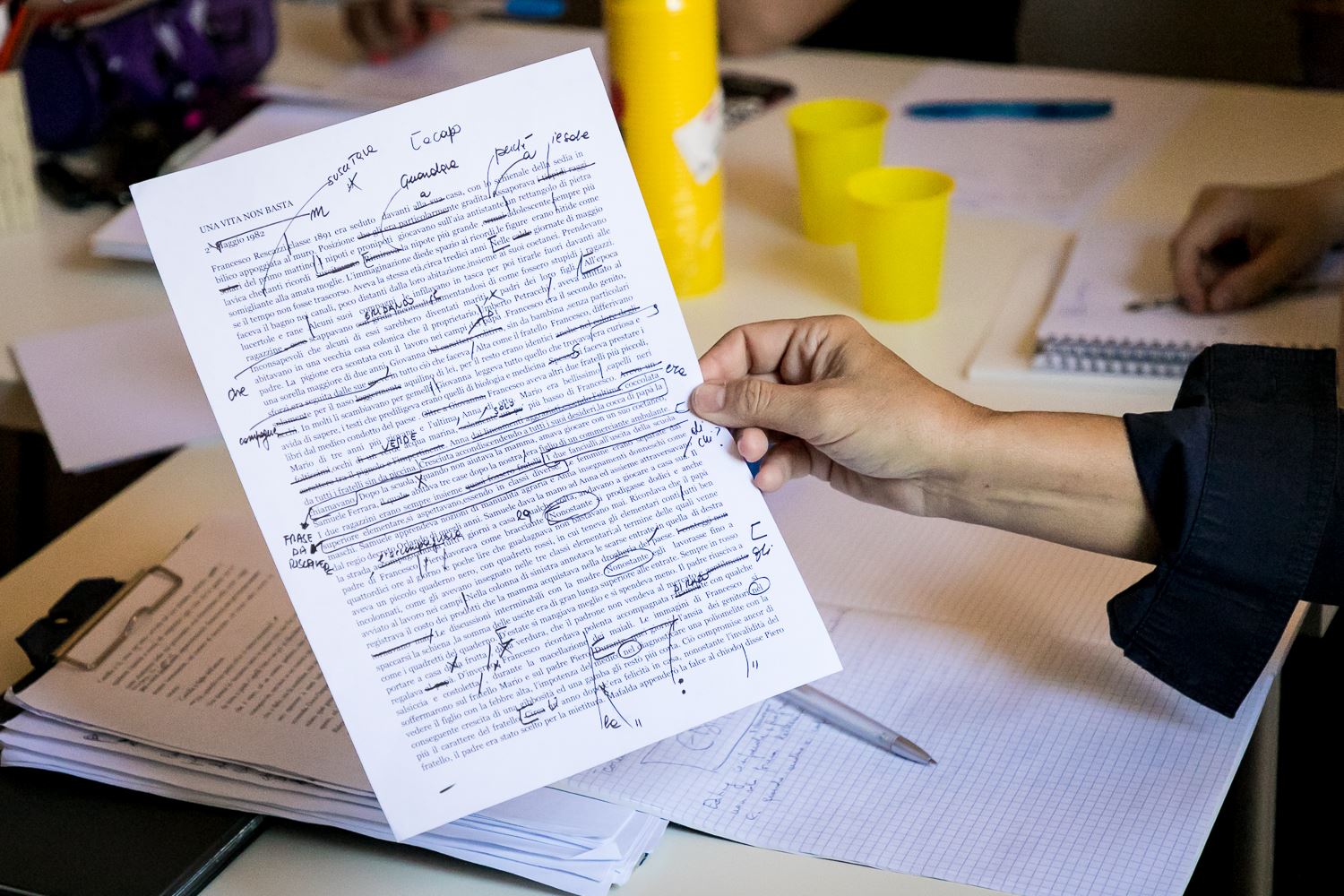
Just drafted your article and can't wait to publish it? Stop dear copywriter, first autocorrect it then we'll talk about it! Now the question is only one: Are you ready to proofread yourself without someone's help? If you opened this post, the answer is right in front of your eyes, don't you think? ...
It's easy to have a nervous breakdown when you're writing content for the web on a regular basis. Sometimes the ideas for writing well don't come and other times you have too many to be able to express them by writing a good online article . But do not worry. The greatest online copywriting experts ...
By accepting you will be accessing a service provided by a third-party external to https://www.insightadv.it/